Write your awesome label here.
CAN Threats and Protections
Assessment of existing threats to CAN devices and systems. Justifications for lightweight protections, including non-cryptographic solutions.
What's covered?
-
OVERVIEW OF KNOWN CAN SYSTEM VULNERABILITIES
Comparing CAN, CAN FD and CAN XL. Manipulations available to attackers with physical or logical access to a CAN system. -
JUSTIFICATIONS FOR MODERATE PROTECTION
Deeply embedded, often constraint devices. Requirement for proportional cost security measures. -
NON-CRYPTOGRAPHIC AND CRYTOGRAPHIC SECURITY MEASURES
From combining zoning/segmentation with secure gateways and security anomaly detection to full authentication and encryption.
Supporting Documents Included
-
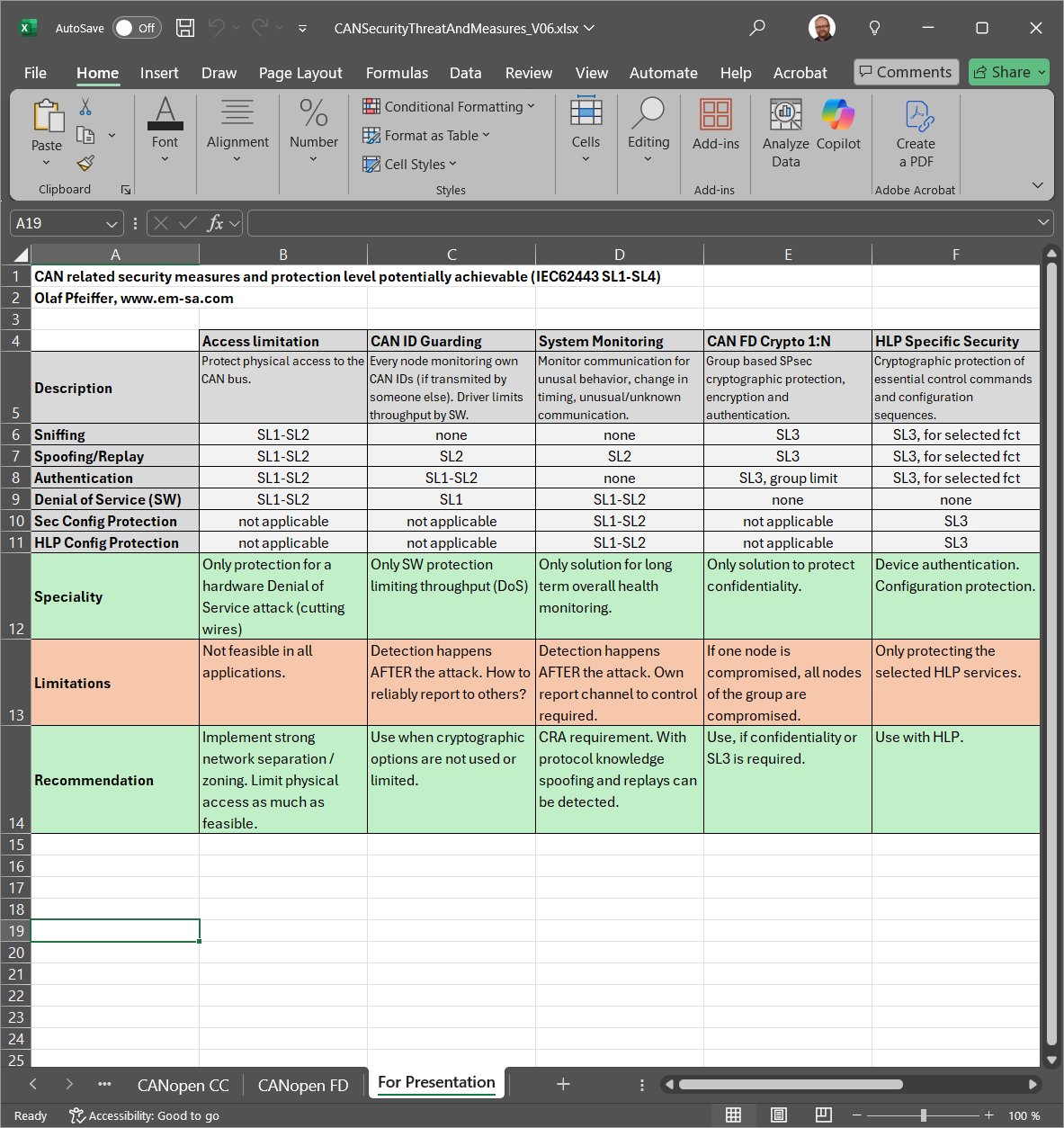
Threats and Measures Overview Table
Overview table (Excel) showing the various threats, potential security measures and how they translate to security levels potentially reachable. -
Cryptographic Measures Overview Table
Overview table (Excel) showing the available cryptographic measures, including lightweight solutions along with their implementation effort and costs.
Olaf Pfeiffer
Olaf Pfeiffer studied technical computer science at the Cooperative University in Karlsruhe. He is one of the founders of the Embedded Systems Academy. Together with his partners, he wrote the books „Embedded Networking with CAN and CANopen“ and „Implementing Scalable CAN Security with CANcrypt“. He is a regular speaker at the international CAN Conferences and other events. Olaf is chairman of several CAN in Automation special interest groups, including the “HLP Cybersecurity”.