Write your awesome label here.
Mapping CRA Requirements to CAN
Review of all requirements of the EU Cyber Resilience Act and how they can be mapped to CAN based applications.
What's covered?
-
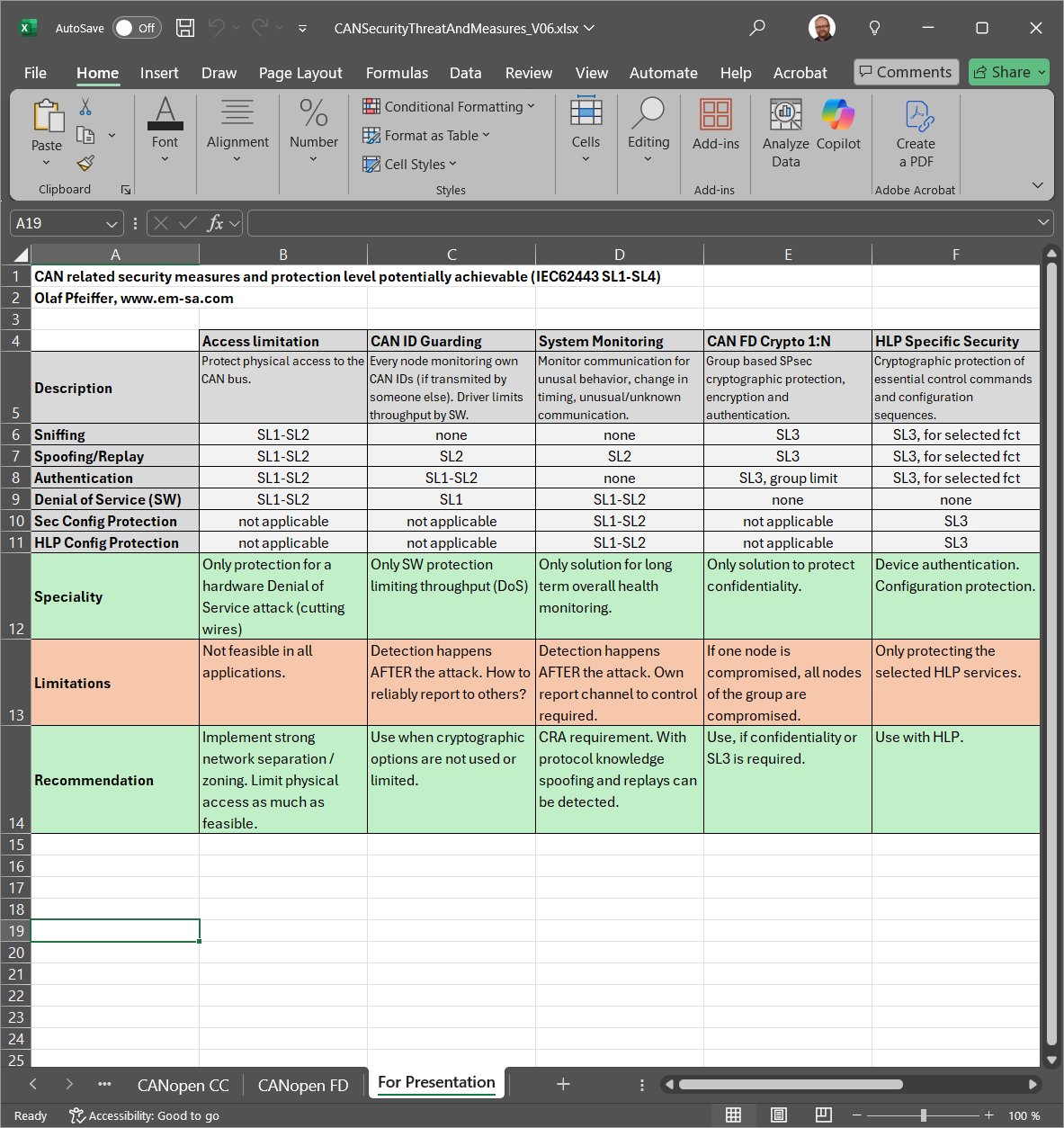
OVERVIEW OF REQUIREMENTS
Overview of the EU Cyber Resilience Act requirements with the biggest impact on products using CAN based communication. -
SECURITY REQUIREMENTS
Review of the security requirements of CRA Annex I and how they can be addressed for CAN products. -
VULNERABILITY HANDLING REQUIREMENTS
Review of vulnerability handling requirements of CRA Annex I and how they must be addressed.
Supporting Documents Included
-
Requirements Overview Table
Overview table (Excel) showing the requirements and actions to be taken. -
Vulnerability Scoring and Reporting Processes
Starting September 2026 manufacturers must start vulnerability reporting for all products with digital elements. Our process guideline shows into which steps the vulnerability handling can be divided and how vulnerabilities involving CAN should be scored using CVSS.
Olaf Pfeiffer
Olaf Pfeiffer studied technical computer science at the Cooperative University in Karlsruhe. He is one of the founders of the Embedded Systems Academy. Together with his partners, he wrote the books „Embedded Networking with CAN and CANopen“ and „Implementing Scalable CAN Security with CANcrypt“. He is a regular speaker at the international CAN Conferences and other events. Olaf is chairman of several CAN in Automation special interest groups, including the “HLP Cybersecurity”.